Disposable email offers instant, anonymous sign-ups to avoid spam, but lacks security and long-term reliability. Real email provides essential security, permanence, and trust for professional and personal life, but requires active management against clutter. Choosing the right tool depends entirely on your specific online activity and risk tolerance.
Ever felt that pang of hesitation when a website asks for your email? You want the free guide, the discount code, or to just see the content, but you don’t want another source of spam clogging your primary inbox. This is the classic modern dilemma. On one side, you have your real email—the one tied to your identity, your bank, your job. On the other, the allure of a disposable email, a throwaway address that vanishes after 10 minutes. But which is better? It’s not about which is universally “good” or “bad.” It’s about understanding the starkly different purposes they serve. This isn’t just a technical comparison; it’s about protecting your privacy, your security, and your sanity in a hyper-connected world. Let’s break down the pros and cons of each, so you never have to guess again.
Key Takeaways
- Disposable email is a temporary tool, not a replacement: Its core strength is privacy for one-time tasks, but it fails for any account needing recovery, longevity, or trust.
- Real email is your digital identity backbone: It’s mandatory for critical services (banking, jobs, main social media) and offers robust security features disposable emails cannot match.
- Spam protection works both ways: Disposable emails *contain* spam to a dead address. Real emails require active filtering but keep your primary address clean from unwanted marketing.
- Security is non-negotiable for sensitive data: Never use a disposable email for passwords, financial records, or official communication. Real email providers invest heavily in encryption and fraud prevention.
- Use case dictates the choice: Downloading a whitepaper? Use disposable. Registering for a company webinar? Use your real email. Context is everything.
- Account recovery is a real email exclusive: Forgot your password? Your recovery email *must* be a permanent, accessible address you control—a disposable one is a one-way ticket to a locked account.
- Professional credibility requires a real address: A @gmail.com or custom domain email builds trust. A random temp mail address destroys it instantly in business or networking contexts.
📑 Table of Contents
What Exactly is a Disposable (Temp) Email?
Before we debate, we must define. A disposable email, often called a temp mail or throwaway email, is a service that provides you with a random, temporary email address. You visit a website like Temp-Mail.org or 10MinuteMail.com, and it generates an address like [email protected]. You use that to sign up for a service, read the confirmation email in the site’s built-in browser inbox, and then… that’s it. The address and all its emails self-destruct, usually within 10 minutes to a few hours. No password, no login, no persistence.
The Core Mechanics: How They Actually Work
These services operate on a simple principle: they create a vast pool of random inboxes. When you visit, they assign you one from the pool. All emails sent to that address are stored on their server temporarily, accessible only via a unique, session-based URL. Once the timer expires or the inbox is cleared, that address is recycled and given to the next user. There’s no personal connection to you. You are a ghost user for a ghost inbox.
The Pros and Cons of Disposable Email
Disposable email is the specialist tool in your digital toolbox. It excels at one job and fails at almost everything else.
Visual guide about Disposable Email Vs Real Email: Pros and Cons
Image source: smartsheet.com
Pros: The Shield Against Digital Clutter
- Instant Spam Containment: This is the #1 reason people use them. You sign up for a sketchy forum, a one-time download, or a site you don’t trust. Any future promotional emails or data breaches are sent to an address that ceases to exist. Your primary inbox remains pristine.
- Zero Commitment, Zero Registration: No need to create an account, set a password, or verify a phone number. You click, get an address, use it, and walk away. It’s the ultimate “no strings attached” for online forms.
- Privacy by Anonymity: Since there’s no account, there’s no personal data (name, birthdate, recovery phone) linked to the address. For whistleblowers, activists in restrictive regions, or anyone wanting to browse a service anonymously, this offers a layer of separation.
- Bypassing Simple Email Blocks: Some forums or websites block known disposable email domains. Using a lesser-known temp mail provider can sometimes bypass these blocks to access a free resource you genuinely need.
Cons: The Critical Weaknesses You Must Know
- No Security, No Encryption: These services are not built for security. Emails are often stored in plain text on their servers. The connection may not be fully encrypted. You are sending potentially sensitive information (like a download link with a license key) over a completely open, unsecured channel.
- No Account Recovery, Ever: You cannot recover a password for an account signed up with a disposable email. The moment the inbox expires, that account is permanently locked. You have effectively thrown away the key.
- Extreme Lack of Reliability: Emails can be delayed, fail to arrive, or be lost if the service’s server has a hiccup. For important confirmations (like a trial subscription activation), this is a gamble you will lose.
- Trust and Credibility Destroyer: Using a temp mail for a professional networking site, a job application portal, or a client meeting scheduler is an immediate red flag. It screams “I have something to hide” or “I’m not serious.”
- Often Blocked by Major Platforms: Gmail, Outlook, Facebook, LinkedIn, and most major SaaS platforms actively block known disposable email domains to prevent fraud and abuse. You simply cannot use them for essential services.
- Potential for Malicious Use: Because they are anonymous, these inboxes are frequently used for signing up to illegal services, sending spam, or creating fake accounts. Your temporary inbox could be the recipient of illicit content, and you have no control over it.
The Pros and Cons of a Real Email Address
Your real email—whether it’s a free service like Gmail or Outlook, or a paid/custom domain address—is your digital passport. It’s expected, required, and foundational to your online existence.
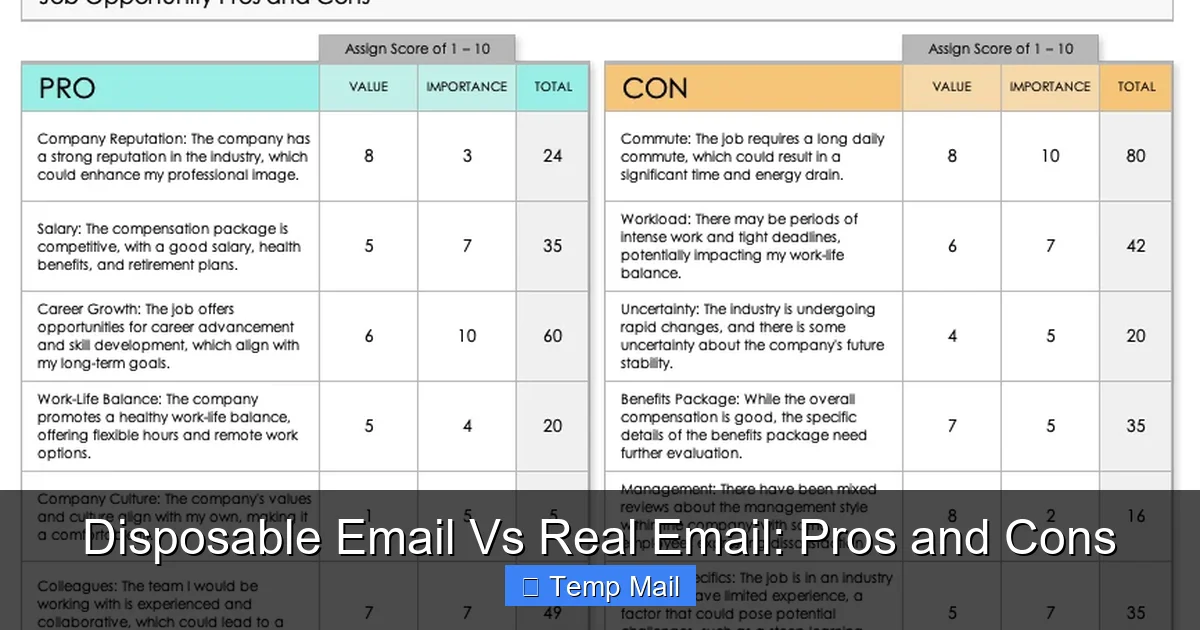
Visual guide about Disposable Email Vs Real Email: Pros and Cons
Image source: smartsheet.com
Pros: The Pillars of Digital Life
- Unquestioned Legitimacy and Trust: A real email address is the global standard for identity verification. It tells websites, employers, and contacts that you are a verifiable person. It’s a prerequisite for almost all meaningful online engagement.
- Robust Security Infrastructure: Major providers invest billions in security. This includes end-to-end encryption (in some services), two-factor authentication (2FA), advanced spam filters powered by AI, phishing detection, and secure account recovery processes. Your data is protected.
- Permanence and Control: You own this address. You control the password. You can access it from any device, anywhere, forever (as long as you maintain the account). It’s your central hub for all important communications.
- Essential for Account Recovery: Every major service uses your email as the primary recovery method. If you forget your password for your social media, bank, or cloud storage, the reset link goes to your real, permanent email. This is non-negotiable.
- Rich Feature Set and Integration: Real emails come with calendars, cloud storage (Google Drive, OneDrive), contact management, task lists, and seamless integration with other productivity tools. They are command centers, not just inboxes.
- Professional and Personal Branding: For business, a custom domain email ([email protected]) is professional gold. Even a polished free address ([email protected]) is infinitely more credible than a temp mail for networking.
Cons: The Inevitable Management Burden
- Spam and Marketing Overload: Your real email is a target. Every data breach, every website you sign up for, can add you to marketing lists. You must actively manage filters, unsubscribe from newsletters, and be vigilant against phishing.
- Privacy Trade-Off: Free email providers scan your emails (in a automated, non-human way) to serve targeted ads. You are trading a degree of privacy for a free, robust service. Your data is their product.
- Permanent Digital Footprint: Every account you create with this email links back to your core identity. A data breach at one site can expose this central identifier, making you a target for credential stuffing attacks on other sites.
- Clutter and Distraction: A busy real inbox can be overwhelming. Important messages get lost in promotional noise, leading to stress and missed opportunities if not managed well.
- Single Point of Failure: If your main email account is hacked, the attacker can initiate password resets for *all* your linked accounts (social media, banking, etc.), causing catastrophic damage. This makes securing your real email paramount.
Security & Privacy: The Deciding Factor
This is where the chasm between the two options becomes a canyon. Security isn’t just about passwords; it’s about the integrity of your communications and the safety of your accounts.
Visual guide about Disposable Email Vs Real Email: Pros and Cons
Image source: nonprofithub.org
How Disposable Emails Fail on Security
Think of a disposable inbox as a public bulletin board in a busy train station. Anyone who knows the URL (which is often simple and predictable) can see the messages. There is no encryption in transit or at rest by the service itself. There is no 2FA. The provider has no incentive or infrastructure to protect your temporary data because it’s not *your* data—it’s a shared, transient resource. Sending any sensitive information—password reset links, personal documents, financial details—through a disposable email is like shouting it across a crowded room.
How Real Emails Build a Security Ecosystem
Your real email is a digital fortress under constant siege. Providers deploy:
- Encryption: TLS for data in transit, and for services like Gmail, encryption for emails stored on their servers.
- Multi-Factor Authentication (MFA/2FA): This is your most critical defense. Even if your password is stolen, a hacker needs your phone or security key to log in.
- Advanced Threat Protection: Real-time scanning for malware in attachments and links. Suspicious login alerts sent to your recovery methods.
- Phishing & Spoofing Defenses: Visual indicators (like a red warning banner) for suspected phishing attempts and authentication protocols (DMARC, SPF, DKIM) that help prevent email spoofing.
The lesson is clear: security is a feature of permanence and investment. Disposable email services have no business model that supports building this level of protection. Your real email provider’s entire reputation depends on it.
Strategic Use Cases: When to Use Which
Knowledge is power, but applied knowledge is results. Here is your practical decision guide.
Use a DISPOSABLE Email For:
- One-time content downloads: E-books, whitepapers, templates where you just want the file and nothing else.
- Signing up for forums or comment sections you’ll rarely use, especially if the site is known for aggressive marketing.
- Testing a service or app with a quick, no-commitment trial that doesn’t require a payment method.
- Accessing a gated article from a publisher you don’t trust or want to hear from again.
- Creating a burner account for a casual, non-personal game or app where your identity doesn’t matter.
Golden Rule: If you wouldn’t want the password reset link to go there, don’t use a disposable email.
Use a REAL Email For:
- Anything financial: Bank accounts, credit cards, PayPal, investment platforms.
- Professional & Academic: Job applications, LinkedIn, university portals, professor communications.
- Primary Social Media: Facebook, Instagram, Twitter/X—your main, personal accounts.
- Cloud Storage & Productivity: Google Drive, Dropbox, Microsoft 365, project management tools.
- Government & Official Services: Tax agencies (IRS), DMV, voter registration, official health portals.
- Any service you intend to use long-term or that holds valuable personal data (photos, documents, messages).
- Account recovery for other services: This is meta, but crucial. Your recovery email for your bank should be a real, secure email you check regularly.
Golden Rule: If losing access to this account would cause significant life disruption, it needs a real email.
Best Practices for Managing Both Worlds
Smart digital citizens don’t choose one or the other exclusively; they use a strategy.
1. The Layered Inbox Strategy
Use your main real email for critical, personal, and professional life. Create a secondary real email (e.g., a free Gmail account) for online shopping, newsletters, and less-critical sign-ups. This contains spam to a separate inbox. Never use your primary bank-account email for shopping sites.
2. The Disposable Discipline
Have a bookmarked tab for your preferred disposable email provider. Use it swiftly and forget it. Do not bookmark the specific inbox URL (it will expire). Do not try to “log in” later—you can’t. Its purpose is served in the moment.
3. Fortify Your Real Email
This is your most important digital asset. Treat it like the keys to your house.
- Enable 2FA immediately. Use an authenticator app (Google Authenticator, Authy) over SMS where possible.
- Use a unique, strong password stored in a password manager (Bitwarden, 1Password).
- Set up a secure recovery email and phone number. This is your lifeline if you get locked out.
- Review connected apps and site permissions every 6 months. Revoke access for anything you no longer use.
4. The “Recovery Email” Rule of Thumb
When signing up for a *new* service, the email you provide is its “username.” The “recovery email” you provide for *that* service should be your main, permanent, secure real email address. This creates a chain of custody: the service emails you at your temp mail, but if you lose access to the service account, the recovery link goes to your fortress email. This is a vital, often overlooked, security layer.
The Verdict: A Toolbox, Not a Battle
The question isn’t “Disposable vs Real.” The question is “What is this online action worth to me?”
A disposable email is a fantastic, low-stakes tool for a specific, low-value transaction: accessing a piece of content you’ll consume once. It’s a privacy filter for the minor leagues of the internet.
Your real email is your sovereign digital territory. It’s where your identity, finances, and critical relationships live online. It requires maintenance and vigilance, but it provides the security, permanence, and trust required for the major leagues of life.
The most empowering approach is to be intentional. Before you type an email into any field, pause for two seconds. Ask: “What’s at stake here?” If the answer is “nothing much, just a quick download,” reach for the temp mail. If the answer is “my identity, my money, my job, or my memories,” use your real, secured email and enable 2FA. This simple habit is one of the most effective digital hygiene practices you can adopt. Use each tool for its designed purpose, and you’ll navigate the web with both convenience and confidence.
Frequently Asked Questions
Can I use a disposable email for important accounts like banking or social media?
Absolutely not. These services require a permanent, secure email for account recovery, security alerts, and legal communication. Using a disposable email will guarantee you lose access to the account permanently.
Are disposable emails truly anonymous?
They offer pseudonymity, not true anonymity. The service provider still logs IP addresses and timestamps. While no personal info is tied to the inbox itself, the activity is not completely hidden from the service operator and could be subject to legal requests.
What happens to my emails in a disposable inbox?
They are permanently deleted from the service’s servers after the time limit expires (usually 10 minutes to a few hours). The email address is then recycled and given to a new, random user. You have no way to retrieve them.
Is it safe to use my real email for all online shopping?
It’s common, but not ideal for maximum security. Using a dedicated secondary real email for shopping helps contain marketing spam and limits exposure if a retailer suffers a data breach. Your primary email should be reserved for finance, identity, and core personal accounts.
Can major platforms detect and block disposable emails?
Yes, actively. Gmail, Outlook, Facebook, LinkedIn, and most reputable SaaS platforms maintain and constantly update lists of known disposable email domains. Attempting to sign up with one will usually be rejected outright.
What is the single most important thing to do for my real email security?
Enable and use Two-Factor Authentication (2FA) with an authenticator app (like Google Authenticator or Authy). This is your strongest defense against password theft and is far more secure than SMS-based codes.
Leave a Reply