Tired of your main email overflowing with spam? Temp mail provides a disposable, anonymous email address for signing up to websites, downloading files, or verifying accounts. It acts as a protective buffer, keeping your real inbox clean, secure, and private. By using a temporary address for low-trust interactions, you eliminate the risk of your primary email being sold, hacked, or bombarded with unwanted messages forever.
Key Takeaways
- Primary Defense: Temp mail creates a sacrificial email address that absorbs spam and promotional emails, protecting your permanent inbox.
- Enhanced Privacy: It prevents websites and services from collecting your real email address, reducing your digital footprint and data profiling.
- Scam & Phishing Shield: By not using your primary email for risky sign-ups, you isolate potential phishing attempts and malware campaigns to a disposable account.
- Simplified Management: No more tedious unsubscribes. Once a temp mail address expires, all associated unwanted mail vanishes automatically.
- No Long-Term Commitment: Use it for a single verification and forget it, with no need to manage another permanent email account.
- Security Through Isolation: A data breach at a low-priority site won’t expose your primary email, preventing credential stuffing attacks on your important accounts.
- Cost-Effective: Most reliable temp mail services are free, offering a powerful privacy tool without any subscription fee.
📑 Table of Contents
- Your Inbox is Under Siege: The Modern Email Problem
- What Exactly is Temp Mail? A disposable shield for your digital life
- The Primary Benefit: A Fortress for Your Primary Inbox
- Beyond Spam: Critical Security Advantages
- Practical Use Cases: When and How to Use Temp Mail
- Choosing a Temp Mail Service: What to Look For
- Debunking Myths: What Temp Mail is NOT
Your Inbox is Under Siege: The Modern Email Problem
Picture this: you finally find that free e-book, exclusive webinar, or must-have discount. You click the sign-up button, enter your email, and hit submit. What happens next? Often, that’s the moment your primary inbox begins its slow, painful descent into chaos. That single email address you use for everything—banking, work, family, Netflix—becomes a commodity. It gets shared, sold, and scraped. Within weeks, your inbox transforms from a useful tool into a battlefield of promotional blasts, “special offers” you never asked for, and sophisticated phishing lures designed to look like they’re from your bank or Amazon. This isn’t just annoying; it’s a serious privacy and security risk. Every data breach at some obscure forum you signed up for a decade ago potentially exposes that one key to your entire digital life. But what if you could fight back? What if you could have a secret weapon that lets you access the internet’s free resources without sacrificing your main communication hub? That weapon is temporary email, or temp mail.
What Exactly is Temp Mail? A disposable shield for your digital life
The Core Concept: An Email Address with an Expiration Date
At its heart, temp mail is beautifully simple. It’s a service that provides you with a random, fully functional email address—complete with an inbox—for a short, predetermined period, usually 10 minutes to 24 hours. You use this address for a specific, low-stakes purpose: verifying an account on a sketchy forum, downloading a software trial, or getting a one-time discount code. Once that purpose is fulfilled, and you’ve received the necessary email, you simply close the browser tab. There is no password, no long-term login, no need to “manage” this account. The address and all its history—including any spam it attracted—vanish into the digital ether. It’s the digital equivalent of using a burner phone, but for your email.
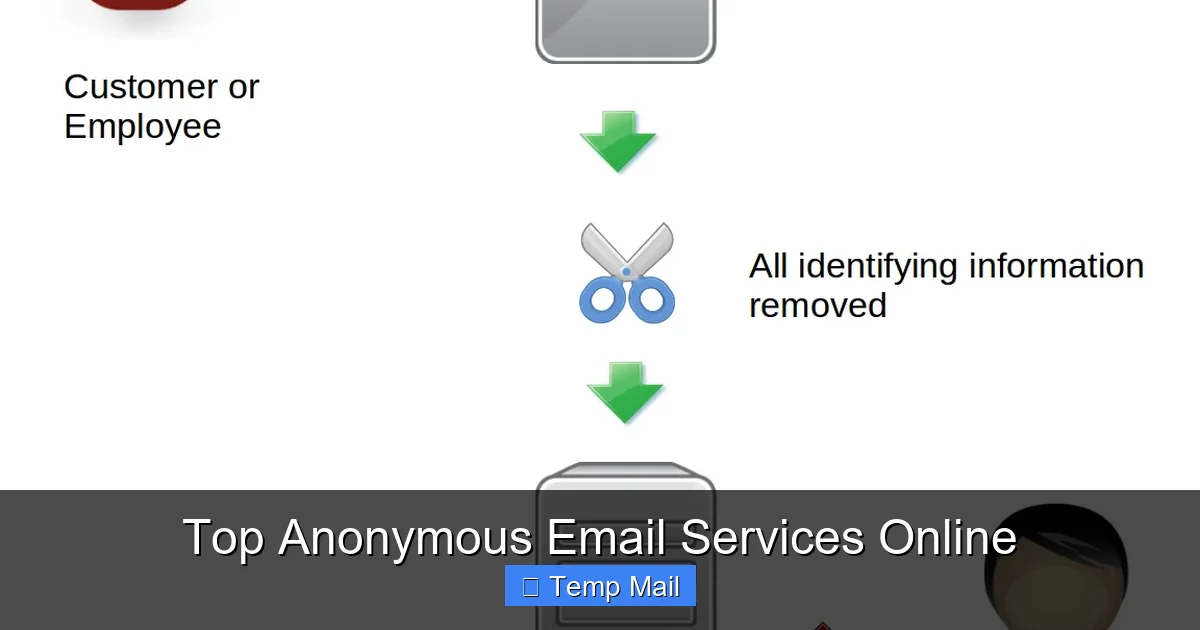
Visual guide about How Temp Mail Protects Your Inbox
Image source: temp-inbox.me
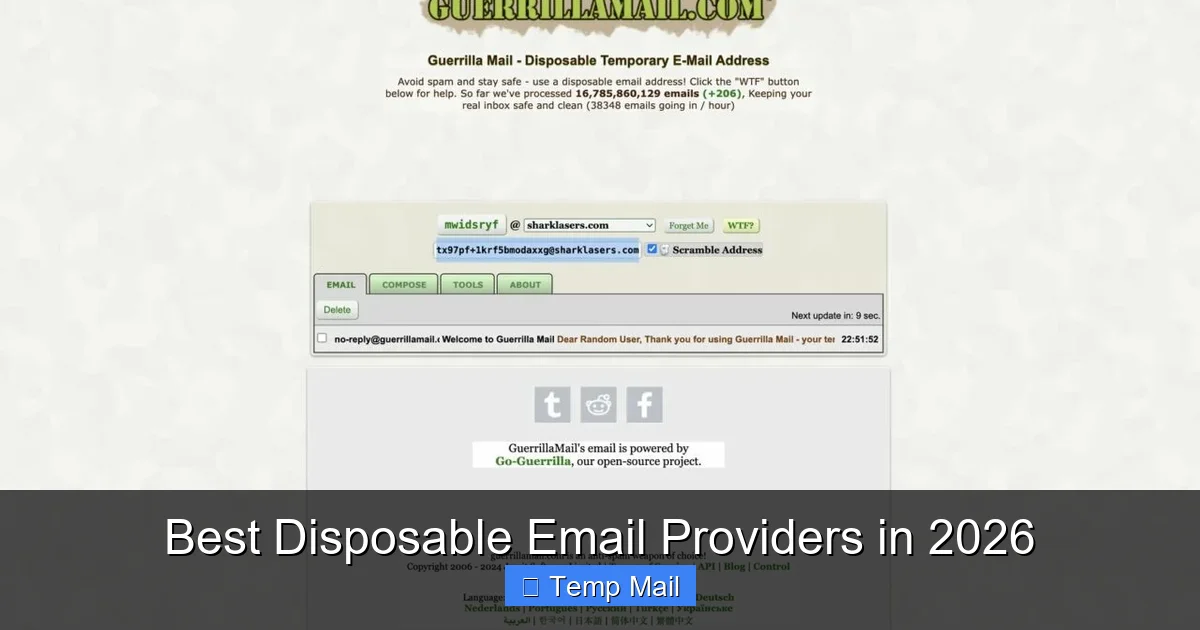
How It Works, Step-by-Step: Simplicity Itself
The process is intentionally frictionless to encourage use. First, you visit a temp mail provider’s website (like Temp-Mail.org, 10MinuteMail, or Guerrilla Mail). The site instantly generates a random email address for you, something like [email protected]. This address is already active and has an inbox waiting. You copy this address and paste it wherever a site asks for your email. You then refresh the temp mail site’s inbox page. When the website you signed up for sends a verification email, it appears right there in your temporary inbox. You click the verification link, complete your task, and walk away. No account creation, no password memorization. The service handles all the backend server work; you just use the interface to view the emails that come in during that address’s short lifespan.
The Primary Benefit: A Fortress for Your Primary Inbox
Stopping Spam at the Source
This is the most immediate and gratifying benefit. Spam doesn’t magically appear; it’s born when you give your email to a service that either has poor data practices or outright sells your address to marketers. By using a temp mail address for any sign-up that isn’t critically important (which is most of them), you redirect that spam pipeline. The unwanted promotional emails, the “newsletter” you accidentally opted into, the aggressive ad campaigns—they all go to the disposable address. When that address expires, the spam dies with it. Your primary inbox, the one you use for real communication with colleagues, family, and essential services, remains a pristine, focused space. You reclaim your attention and your time.
Visual guide about How Temp Mail Protects Your Inbox
Image source: temp-inbox.me
Creating an Ironclad Privacy Barrier
Your email address is a unique personal identifier. It’s often the username for dozens of other accounts. When you use it everywhere, you create a comprehensive, linked profile of your online behavior that data brokers and advertisers can buy. Temp mail shatters this profile. For every minor interaction, you use a new, unlinked identifier. This makes it exponentially harder for companies to track you across the web, build a dossier on your interests, and target you with invasive ads. You are, in effect, anonymizing your casual internet activity, taking back control of your digital identity piece by piece.
Beyond Spam: Critical Security Advantages
Neutralizing Phishing and Scam Emails
Phishing emails are designed to look like they’re from a trusted entity—your bank, PayPal, a popular store—and they urge you to click a link and log in. The damage occurs when you use your real credentials on a fake site. By using temp mail for non-essential sign-ups, you create a crucial mental filter. If you receive a “security alert” or “account issue” email to your primary inbox, it immediately raises a red flag because you know you only use that address for vital accounts. But if you used temp mail for a gaming site and get a “password reset” email there a year later, you know it’s a scam targeting old data. It trains you to be more skeptical and isolates phishing attempts to accounts with no valuable data attached.
Visual guide about How Temp Mail Protects Your Inbox
Image source: is1-ssl.mzstatic.com
Containing the Fallout from Data Breaches
Data breaches are a matter of “when,” not “if.” Every few months, another major company announces hackers stole user databases, including email addresses. When your temp mail address is part of a breach, nothing of value is lost. It’s a dead letter. However, when your permanent email is breached, hackers now have a key to your identity. They can use it to try to reset passwords on your other accounts (a tactic called “credential stuffing”), send highly targeted phishing emails, or sell it on the dark web for identity theft. Temp mail ensures that the vast majority of your low-importance online interactions leave no lasting trace that can be weaponized against you later.
Practical Use Cases: When and How to Use Temp Mail
For One-Time Access & Gated Content
This is the #1 use case. A blog offers a valuable PDF checklist in exchange for an email. A forum requires registration to view a single thread. A software site offers a trial download but demands an email for the license key. These are perfect moments for temp mail. You get the content or tool you need, and the provider gets a metric (a sign-up), but you give away nothing of lasting value. You avoid being added to their nurturing email sequence forever.
For Testing Services and Apps
Are you a developer testing user registration flows? A marketer checking how a lead magnet delivery system works? Or just a curious user wanting to poke around a new app without commitment? Temp mail is your best friend. You can create a test account, verify it, explore the features, and never have to worry about cleaning up the account later or receiving product update emails.
To Protect Your Identity on Forums and Comment Sections
Participating in a heated political forum, a niche hobby subreddit, or a controversial news comment section? Using your primary email ties your real-world identity to your pseudonymous opinions. A temp mail address lets you engage in discussion with a layer of plausible deniability. If the account is banned or the forum is compromised, your main email remains unaffected and unlinked.
Choosing a Temp Mail Service: What to Look For
Essential Features: Inbox Lifespan and Domain Variety
Not all temp mail services are created equal. The first thing to check is the default inbox lifespan. Some offer 10 minutes (for ultra-quick tasks), others 1 hour, and some up to 24 hours. Choose based on your need. For a quick download, 10 minutes is fine. For a forum that might send a welcome email a few hours later, go for a longer duration. Also, look at the available domains (@tempmail.net, @guerrillamail.com, etc.). A wider variety can be useful if a particular site blocks known temp mail domains (some do).
Advanced Considerations: No Password? No Problem.
Remember, the core of temp mail is no account. You should never need to create a password or set up a username. If a service asks you to register to get a temp address, it’s defeating the purpose. You want a site where the inbox is tied to the browser session or a random token. Also, consider the user interface. Is the inbox easy to read? Does it refresh automatically? Are there intrusive ads? A clean, functional interface makes the experience much smoother. For most users, sticking with well-known, reputable providers is safer than obscure ones that might inject malicious scripts.
Debunking Myths: What Temp Mail is NOT
Myth 1: “It’s Only for Illegal Activities”
This is a common misconception. While it’s true bad actors might use it for anonymity, the overwhelming majority of temp mail users are perfectly legitimate people trying to manage their privacy and inbox hygiene. It’s a tool for defensive privacy, not offensive wrongdoing. Using it to avoid a newsletter is not illegal; it’s good inbox stewardship.
Myth 2: “It’s Completely Secure for Sensitive Communications”
This is critical. Temp mail is for low-risk, non-sensitive interactions only. Never use it for password recovery on your main accounts, for official government or banking correspondence, or for sending confidential documents. The emails are stored on the provider’s servers, often unencrypted, and are publicly accessible via the inbox URL while active. It is a public, temporary drop-box. Its security model is based on ephemerality, not encryption or access control.
Myth 3: “All Temp Mail Gets Blocked by Major Sites”
While some major platforms (like Google or Facebook) actively block known disposable email domains, thousands of smaller websites, forums, blogs, and SaaS tools do not. The blocking arms race is constant, but for the vast ecosystem of the web where you need to “just get in,” temp mail remains highly effective. If one domain is blocked, refreshing the page on the temp mail site will often generate a new address from a different, unblocked domain.
Frequently Asked Questions
Is using temp mail legal?
Yes, using a temporary email service is completely legal in virtually all jurisdictions. It is a legitimate tool for privacy protection and managing online subscriptions.
How long do temp mail addresses and emails last?
It varies by provider, but most temporary inboxes last between 10 minutes and 24 hours. After that time, the address and all emails within it are permanently deleted from the server.
Can I send emails from a temp mail address?
Generally, no. Temp mail services are designed primarily for receiving verification and transactional emails. Sending capabilities are usually disabled to prevent abuse for spam.
Is temp mail secure? Can anyone see my emails?
Security is limited. While in transit, emails may not be encrypted. Most importantly, anyone with the unique inbox URL can view all emails in that temporary inbox. This is why it should never be used for sensitive personal or financial information.
Why would a website block a temp mail domain?
Sites block disposable email domains to prevent fake accounts, spam registrations, fraud, and abuse of free trials or promotions. They want to ensure users are providing a real, persistent contact method.
What happens if I need an email after the temp address expires?
Once the temporary inbox expires, the emails are gone forever and cannot be recovered. This is why it’s crucial to only use temp mail for situations where you need the information immediately (like a verification code or download link).